Cisco Meraki MX Client VPN Settings
The client VPN service uses the L2TP tunneling protocol and can be deployed without any additional software on PCs, Macs, iOS devices, and Android devices, since all of these operating systems natively support L2TP VPN connections.
Client VPN Server Settings
To enable Client VPN, choose Enabled from the Client VPN server pulldown menu on the Security Appliance > Configure > Client VPN page. You can configure the following Client VPN options:
- Client VPN subnet: The subnet that will be used for Client VPN connections. This should be a private subnet that is not in use anywhere else in your network. The MX will be the default gateway on this subnet and will route traffic to and from this subnet.
- DNS Nameservers: The servers VPN Clients will use to resolve DNS hostnames. You can choose from Google Public DNS, OpenDNS, or specifying custom DNS servers by IP address.
- WINS: If you want your VPN clients to use WINS to resolve NetBIOS names, select Specify WINS Servers from the drop-down and enter the IP addresses of the desired WINS servers.
- Secret: The shared secret that will be used to establish the Client VPN connection.
- Authentication: How VPN Clients will be authenticated (see below).
Authentication
Meraki Client VPN uses both pre-shared key based authentication and user authentication. To setup the user authentication mechanism, you will need to select your authentication method.
Meraki Cloud Controller authentication
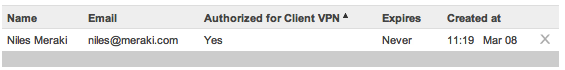
Use this option if you do not have an Active Directory or RADIUS server, or if you wish to manage your VPN users via the Dashboard. To add or remove users, use the User Management section at the bottom of the page. Add a user by clicking "Add new user" and entering the following information:
- Name: Enter the user's name.
- Email: Enter the user's email address.
- Password: Enter a password for the user or click "Generate" to autogenerate a password.
- Authorized: Select whether this user is authorized to use the Client VPN.
To edit an existing user, click on the user under the User Management section. To delete a user, click the X next to the user on the right side of the userlist.
Important
When using Meraki hosted authentication, the user's email address is the username that is used for authentication.
RADIUS
Use this option to authenticate users on a RADIUS server. Click Add a RADIUS server to configure the server(s) to use. You will need to enter the IP address of the RADIUS server, the port to be used for RADIUS communication, and the shared secret for the RADIUS server.
Active Directory
Use this option if you want to authenticate your users with Active Directory domain credentials. You will need to provide the following information:
- Short domain: The short name of your Active Directory domain.
- Server IP: The IP address of an Active Directory server on the MX LAN.
- Domain admin: The domain administrator account the MX should use to query the server.
- Password: Password for the domain administrator account.
For example, considering the following scenario: You wish to authenticate users in the domain test.company.com using an Active Directory server with IP 172.16.1.10. Users normally log into the domain using the format 'test/username' and you have created a domain administrator account with the username 'vpnadmin' and the password 'vpnpassword'.
- Your Short domain would be 'test'.
- Your Server IP would be 172.16.1.10.
- Your Domain admin would be 'vpnadmin'.
- Your Password would be 'vpnpassword'.
For detailed instructions on how to configure a client VPN connection on various client device platforms, please refer to: